Russia and Microsoft have blamed the United States government’s NSA secret program for the WannaCry “Ransomware” attacks that crippled global computer systems with more expected to come. Over 150 countries, 100 thousand organizations and over 200 thousand computers worldwide were impacted by massive cyber-attacks since Friday.
Officials across the globe scrambled over the weekend to protect their systems while trying to catch the perpetrators behind the attacks. The massive ransomware disrupted operations at hospitals, schools, factories, universities including organizations and businesses of all sizes.
The massive cyber attack which began on Friday is believed to be the biggest online extortion in history. The unprecedented global “ransomware” spread chaos by locking computers of Germany’s railway system, Britain’s NHS hospital network, factories and government agencies worldwide.

Over 100 countries were affected has their systems breached by cyber attack and data breach on Friday May 12, 2017.
President Putin said Russia had “nothing to do” with the attacks but blamed the United States for creating the hacking software that was later stolen and leaked, a situation that has resulted in global Microsoft systems computers being impacted.
Speaking to the media in Beijing Putin said, “Malware created by intelligence agencies can backfire on its creators.” He added that global leaders needed to discuss cyber security at a “serious political level” and said the US has backed away from signing a cyber security agreement with Russia.
Microsoft was quick to blame its own US government for developing the ‘Eternal Blue’ exploit which was stolen and leaked to WikiLeaks resulting in the wave of global cyber-attacks. Microsoft also blames the government for not disclosing more software vulnerabilities.
“The governments of the world should treat this attack as a wakeup call,” wrote Brad Smith, Microsoft President in a blog. “This attack provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem.”

Ransomware takes control of your system when locks and boots you out then demanding a ‘ransom’ to be paid to restore your system back. Credit:EPA
Smith then pointed out to a recent theft of CIA hacking tools which were later published by WikiLeaks as proof that NSA losing the Eternal Blue tool was not a one-off incident, comparing the government’s losing of sensitive hacking tools to having cruise missiles stolen.
“Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage. An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen.
“We need government to consider the damage to civilians that comes from hording these vulnerabilities and the use of these exploits,” Smith wrote in the blog.
Cyber security experts said the spread of the worm dubbed WannaCry – “ransomware” that locked up more than 200,000 computers worldwide had slowed but that the respite might only be brief amid fears new versions of the worm will strike.

The WannaCry or “Ransomware” locks the system and then demands victims to pay ransom in hundred of dollars to have their systems restored, the biggest cyber extortion in history. A German railway station that was attacked. Credit: AFP
In a blog post on Sunday, Microsoft President Brad Smith appeared to tacitly acknowledge what researchers had already widely concluded: The ransomware attack leveraged a hacking tool, built by the U.S. National Security Agency, that leaked online in April.
“This is an emerging pattern in 2017,” Smith wrote. “We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world.”
He also poured fuel on a long-running debate over how government intelligence services should balance their desire to keep software flaws secret – in order to conduct espionage and cyber warfare – against sharing those flaws with technology companies to better secure the internet.
“This attack provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem,” Smith wrote. He added that governments around the world should “treat this attack as a wake-up call” and “consider the damage to civilians that comes from hoarding these vulnerabilities and the use of these exploits.”
The NSA and White House did not immediately respond to requests for comment about the Microsoft statement.
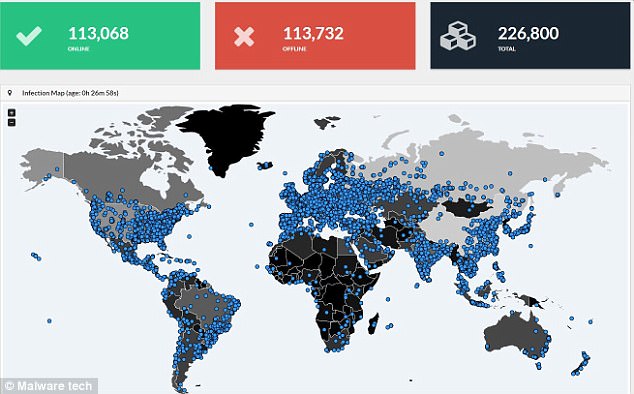
Cyber attacks affected over 150 countries, 100 thousand organizations and over 200 thousand computers worldwide and still growing. Credit:Malware tech
U.S. President Donald Trump on Friday night ordered his homeland security adviser, Tom Bossert, to convene an “emergency meeting” to assess the threat posed by the global attack, a senior administration official told Reuters.
The original attack lost momentum late on Friday after a security researcher took control of a server connected to the outbreak, which crippled a feature that caused the malware to rapidly spread across infected networks.
Infected computers appear to largely be out-of-date devices that organizations deemed not worth the price of upgrading or, in some cases, machines involved in manufacturing or hospital functions that proved too difficult to patch without possibly disrupting crucial operations, security experts said.
Microsoft released patches last month and on Friday to fix a vulnerability that allowed the worm to spread across networks, a rare and powerful feature that caused infections to surge on Friday.
Code for exploiting that bug, which is known as “Eternal Blue,” was released on the internet last month by a hacking group known as the Shadow Brokers.
Had it not been for a young cybersecurity researcher’s accidental discovery of a so-called “kill switch,” the malicious software likely would have spread much farther and faster. Security experts say this attack should wake up every corporate board room and legislative chamber around the globe.
REUTERS
All Edits by Manyika Review. All Rights Reserved.